E-signature vs digital signature — these terms often get mixed up, but they’re far from identical.
In our increasingly digital world, signing PDF or other documents electronically has become second nature, yet the technology behind the methods varies significantly. Both simplify the process of approving contracts and agreements without paper, but differ in how they work and the level of security provided.
Whether you’re trying to choose the best option for your business or simply want to understand the distinction, this article will break down the key differences and explain why knowing them is crucial.
What is an e-signature?
An electronic signature is a digital mechanism used to capture an individual’s intention to approve or accept the contents of a pact.
Unlike traditional handwritten wet signature, e-signatures cover a broad spectrum of options—ranging from simple actions such as typing a name or selecting an "I agree" option, to sophisticated techniques like biometric authentication or cryptographically protected devices.
Legal Framework
E-signatures carry statute validity under regulations such as the ESIGN Act in the United States and the eIDAS Regulation within the European Union. These laws endorse that electronic approvals have equivalent enforceability to physical ones, provided they:
- Clearly demonstrate the approver's intent
- Establish a verifiable connection between the autograph and the document
- Asert the signer’s treaty to use electronic means
Technical Components
The assurance of authenticity and data integrity depends largely on the system enabling the electronic document signing process. Some implementations rely on basic verification, while others incorporate advanced protective measures including:
- Identity ratification via email, SMS, or multi-factor authentication
- Comprehensive audit logs registering the signing steps
- Time-stamped entries to detect any post-validation modifications
- Detailed session records capturing subscriber activity
Since the underlying technology differs greatly among solutions, the resistance to fraud and repudiation varies accordingly.
Types of e-signatures
| Kind | Characteristics | Application |
|---|---|---|
| Simple Electronic Signature (SES) | - Utilizes straightforward methods such as name entering, inserting an image, or selecting a confirmation button. - Security protocols are minimal and depend on platform policies. - Lacks cryptographic safeguards or proof mechanisms, making it suitable for non-critical approvals. | - Everyday agreements - Informal consents - Internal workflows |
| Advanced Electronic Signature (AES) | - Incorporates techniques that distinctly associate the signature with the individual, often involving biometric identifiers or secure credentials. - Includes functions to see any alterations after signing. - Frequently employs asymmetric encryption to ensure authenticity and author exclusivity. | - Commercial contracts - Transactions requiring moderate affirmation - Legal documents |
| Qualified Electronic Signature (QES) | - Deploys specialized software certified to meet strict regulatory requirements. - Supported by digital certificates from accredited authorities, it delivers the highest level of assurance and validity recognized under rigorous standards. | - Statutory submissions - Sectors with strict compliance needs - Critical contractual settlements |
How to create an electronic signature?
1. Choose a Trusted Platform
Opt for a provider licensed under ISO/IEC 27001 that leverages secure communication protocols such as TLS 1.2 or higher. The system should utilize role-based permissions and integrate hardware security modules (HSMs) for safeguarding encryption keys.
Popular PDF e-signature services:
- DocuSign
- Adobe Sign
- HelloSign
- SignNow
- PandaDoc
2. Prepare the Document to Sign Electronically
Upload the target file, commonly in PDF/A, DOCX, or XML format. Implement interactive tags compliant with standards like Form Fields or XFA to specify input locations, ensuring structured data capture.
3. Verify the Identity of the Endorser
Apply measures appropriate to transaction sensitivity, including:
- Single-use passcodes delivered via email or SMS
- Multi-factor authentication utilizing software tokens or smartcards
- Integration with profile management systems supporting SAML 2.0, OAuth 2.0, or OpenID Connect
4. Generate the Esign Documents Mark
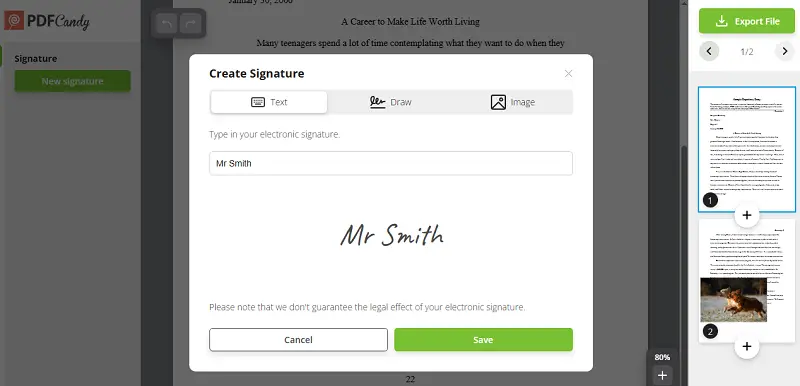
The approver can create their endorsement by:
- Drawing a high-resolution, vector-based signature on touchscreen or input devices
- Entering a name converted into a autograph-style font
- Adding digital certificates aligned with X.509, with private keys stored securely via PKCS#11-compliant modules
5. Link PDF E-Signature to File
Employ cryptic functions such as SHA-256 to make a unique fingerprint of the document. This digest is then encrypted with the element using algorithms like RSA (2048-bit or higher) or ECDSA (secp256r1), establishing proof of immutability.
6. Record Comprehensive Metadata
Log details including:
- Network address and device characteristics
- Authentication techniques employed
- Exact version of the file hashed and signed
- Chronology of user actions for audit and compliance verification
What is a digital signature?
PDF digital signature represents a cryptographic solution designed to confirm the origin and maintain the integrity of electronic information. It employs a pair of asymmetric keys. Private one exclusively controlled by the originator and a publicly available used for validation—to uniquely associate the approval with the specific content.
Legal Recognition
Across global legal frameworks, digital signatures are granted full juridical status when backed by authorized certification entities. Their validity depends on:
- Algorithmic evidence uniquely connecting the consent to the author
- Assurance that the content remains unchanged following the endorsement
- Statutory provisions that enforce signer responsibility and prevent denial of authorization
Technical Components
This technique involves producing a concise representation of the source data, which is then encoded with the proposer’s exclusive key, creating the signature. Legitimacy is verified by decrypting the mark with the corresponding public credential and matching the resulting hash against a freshly generated digest of the received material.
Supplementary protections include:
- Implementation of PKI
- Credible timestamping to document the exact signing moment
- Mechanisms to revoke certificates in cases of compromise
Collectively, these elements provide a resilient framework that guarantees truthfulness, affirms agreement, and guards against falsification or unauthorized modifications.
Types of PDF digital signature
| Find | Characteristics | Application |
|---|---|---|
| Basic | - Relies on asymmetric cryptography without external validation. - Provides figures integrity and signer identification but limited recognition. - Keys usually self-generated without third-party signature makers. | - Internal communications - Low-risk approvals - Testing environments |
| Certified | - Issued by trusted Certificate Authorities verifying the credentials. - Uses X.509-compliant licenses. - Associates public codes with authenticated identities. - Often integrated into Public Key Infrastructure. | - Official documents - Business agreements - Financial transactions |
| Qualified | - Meets stringent regulatory requirements. - Created via secure signature devices such as hardware tokens. - Offers the highest assurance of authenticity and file protection. - Equivalent to handwritten autographs in many jurisdictions. | - Government filings - Legal contracts |
| Biometric | - Combines methods with physiological metrics like fingerprints or voice recognition. - Strengthens ID verification. - Limited usage due to privacy and implementation complexity. | - High-security sectors - Sensitive data access - Identity authentication |
| Remote | - Created through cloud-based or offsite services. - Private tokens managed by third parties. - Enables signing without physical components. - Depends on strong access controls and protocols. | - Mobile workforces - Distributed teams - Digital contract signing |
How to create a digital signature?
1. Obtain a Certificate
- Acquire a credential from a an accredited entity that validates you or that of your business
- Depending on jurisdiction or frameworks, confirmation may involve biometric checks or online ratification
2. Generate a Key Pair
Produce two linked cryptographic elements:
- A private key used for signing
- A public counterpart shared for validation
Key creation can take place in:
- Trusted PDF software tools
- Dedicated hardware (e.g., HSMs)

3. Employ a Digital Signature App
Select a reliable platform that supports:
- X.509
- PKI integration
- Import or access the document directly through the interface
4. Apply the Signature
The system will:
- Create a unique hash of the file
- Add digital signature to PDF
Digital vs electronic signature: comparison table
Here’s a concise table showing difference between digital signature and electronic signature:
| Aspect | E-Signature | Digital Signature |
|---|---|---|
| Definition | Electronic method to express consent or approval | Cryptographic process ensuring authenticity and integrity |
| Purpose | Captures user agreement | Confirms identity and guarantees document integrity |
| Technology Used | Ranges from simple inputs (typed name, checkbox) to advanced methods | Employs Public Key Infrastructure (PKI) and encryption algorithms |
| Legal Standing | Recognized under laws like ESIGN, eIDAS | Considered a secure, advanced variant with higher assurance |
| Security Level | Varies from basic to moderate depending on implementation | Offers robust protection through encryption and certificate validation |
| Verification Method | May depend on audit logs or third-party checks | Requires validation through trusted certificate authorities |
| Typical Use Cases | Approving contracts, agreements, forms | Signing official papers, regulatory documents, software code |
| User Interaction | Simple steps such as clicking “I agree” or drawing signature | Involves key pair generation and cryptographic operations |
| Tamper Evidence | Limited or platform-dependent | Includes built-in mechanisms to detect alterations |
Conclusion
To wrap up, both digital signatures and e-signatures play crucial roles in advancing paperless workflows, yet they fulfill different purposes.
Recognizing these distinctions helps organizations and individuals choose the right solution to align with their compliance, security, and operational goals in today’s digital environment.




